Reviewing pull requests is part of the safety net around Spring Boot backend services. Each merge into the main branch can nudge HTTP endpoints, database behavior, logging, or metrics in small or large ways, and those changes travel with live traffic into production. Short checklists for pull requests keep attention on real runtime behavior instead of style arguments and help junior and senior engineers focus on the same specific checks.
Why Pull Request Checklists Matter For Spring Boot Services
Spring Boot backends usually sit between clients and data stores, with layers such as controllers, services, repositories, and HTTP or messaging clients in between. A single pull request can touch one or several of these layers and change how a request travels from the HTTP edge down to the database and back again. Reviewers who follow a short, repeatable checklist keep both structure and runtime behavior in view instead of reading only a narrow slice of code.
Pull requests also record the story of how a Spring Boot service changed across features and incidents. When production issues appear later, engineers tend to open the most recent pull requests around the affected area and read through tests, comments, and code changes. Checklists that ask about tests, logs, metrics, and documentation give that history more practical value than a stream of unstructured changes and rushed approvals.
How Backend Changes Flow Through The Stack
Web services built on Spring MVC in a Spring Boot project usually follow a predictable route for each HTTP call. A client sends a request, a controller method receives it through an annotation such as @GetMapping, a service method performs business logic, and a repository or client class talks to a database or remote system. Pull requests that touch that chain can introduce subtle shifts in control flow even with a small patch.
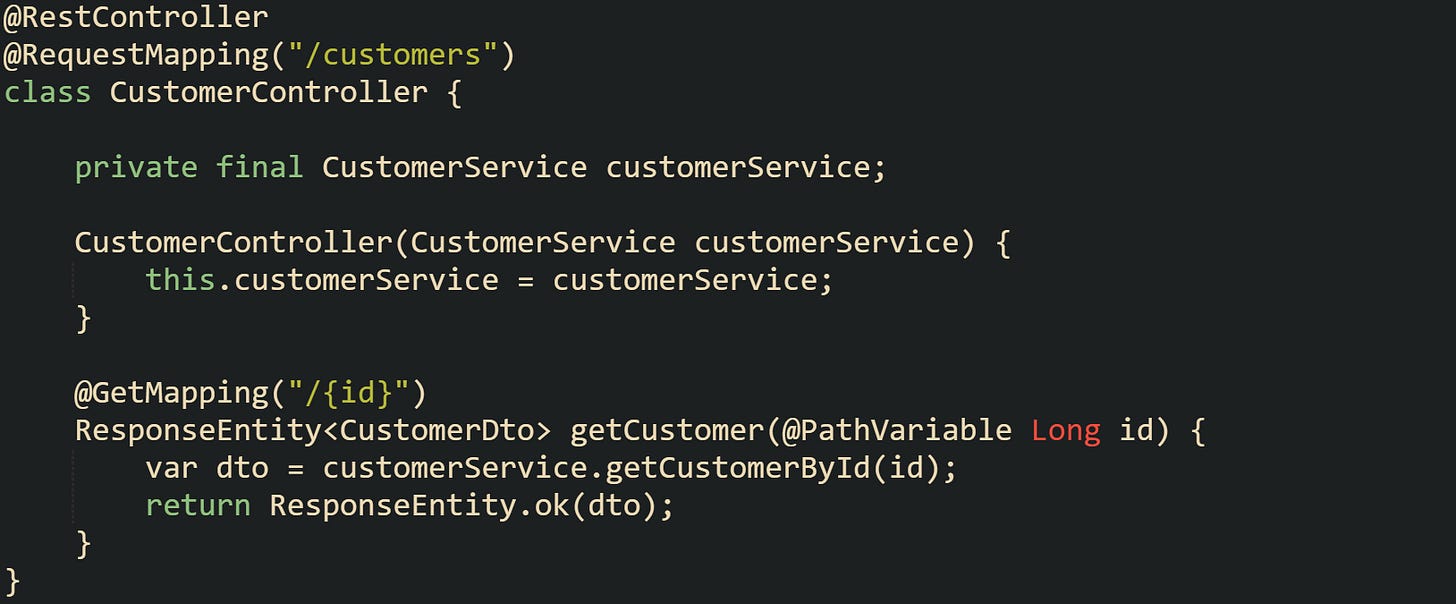
This is what a common controller in a Spring Boot project often looks like:
This controller forwards work to a service class and keeps HTTP specific details such as the URL pattern and response status local to the web layer.
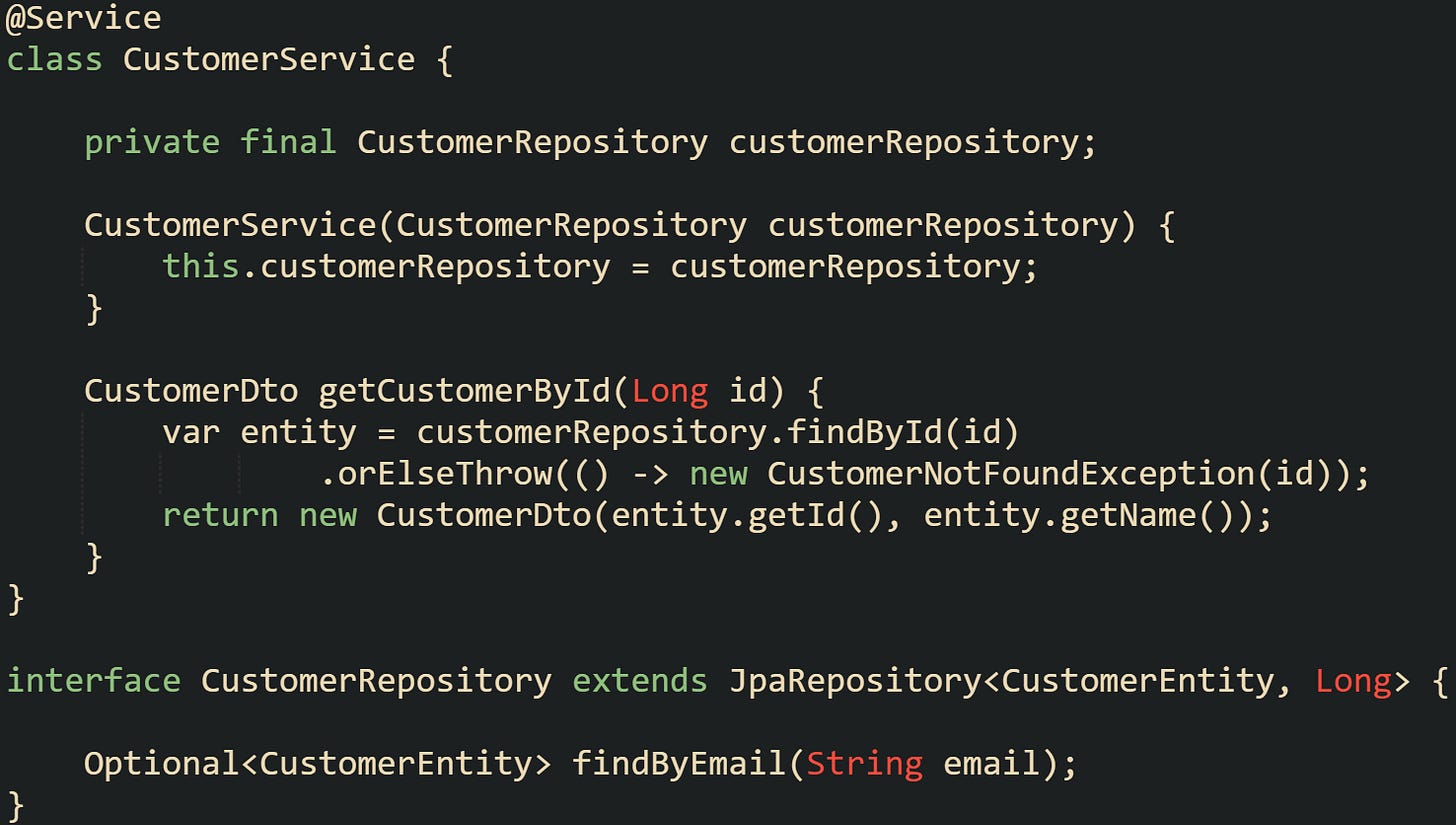
Service and repository classes form the next part of the chain:
This service method calls a Spring Data JPA repository, translates entities into a data transfer object, and raises a domain specific exception when a record is missing. Pull requests that change logic in getCustomerById, swap out the repository interface, or refactor the DTO can affect both correctness and performance.
Small edits to controller annotations can shift behavior in ways that are easy to overlook during a quick review. Changing @RequestMapping("/customers") to @RequestMapping("/client") alters the public API surface. Reviewers with a checklist in mind will cross check URL patterns with API documentation, tests, and client expectations rather than only scanning for syntax errors.
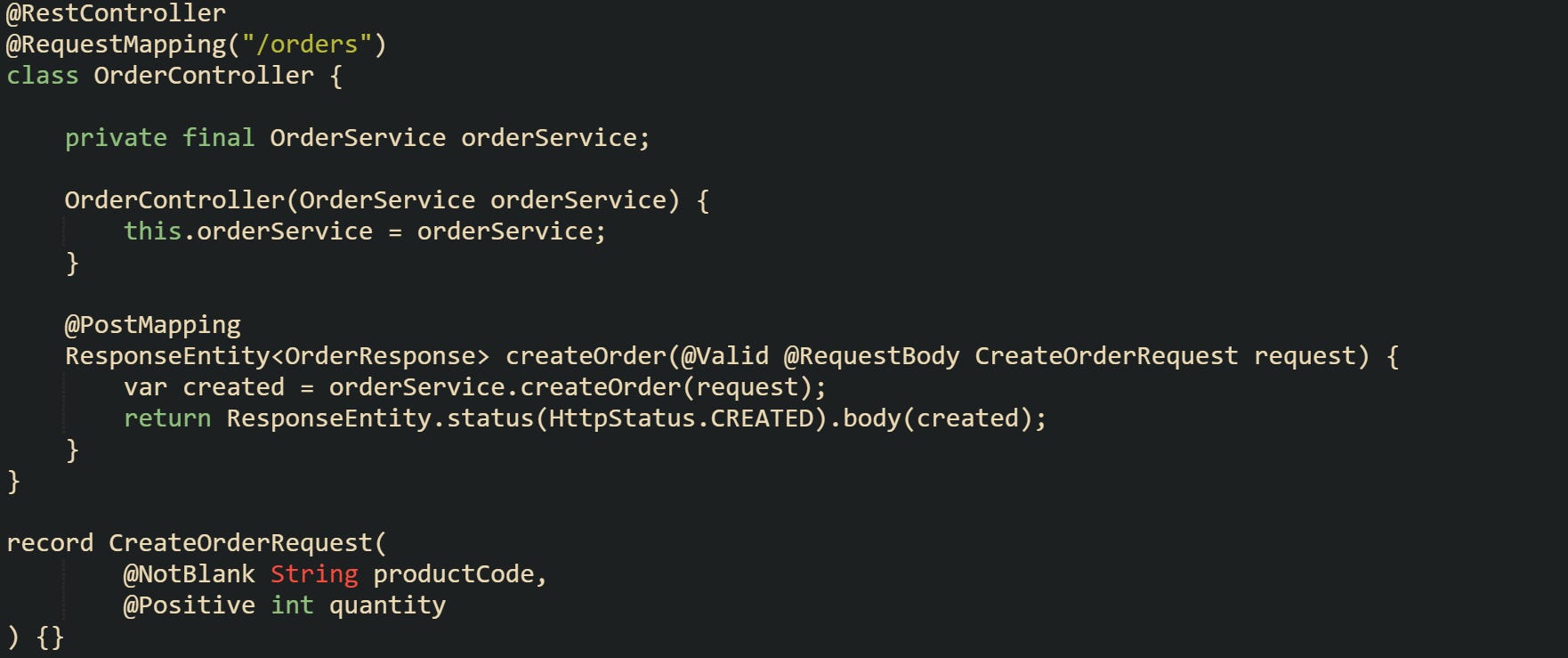
Validation forms one more layer where pull requests have wide impact. Controllers that accept JSON input often rely on Bean Validation annotations and a @Valid parameter:
Any pull request that modifies CreateOrderRequest or removes @Valid changes how invalid input is handled at the HTTP boundary. A checklist that reminds reviewers to scan validation annotations helps catch missing constraints and mismatches between request models and business rules before they reach production.
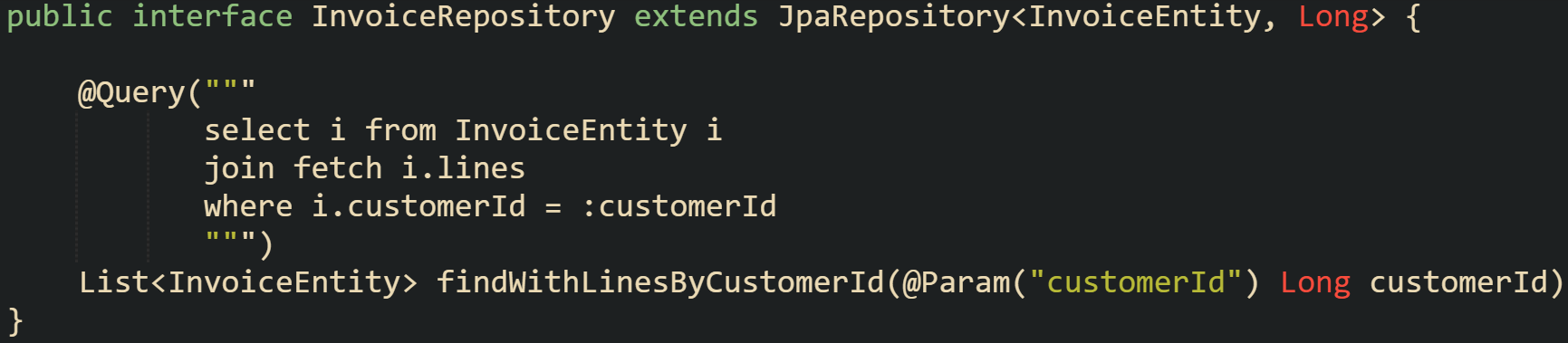
Database access and transactions also sit in this stack. Some repository methods can look harmless during review yet add unexpected load or change isolation behavior.
Replacing a lazy fetch with a join fetch in a pull request can remove N+1 problems on one screen while increasing memory pressure for customers with large invoice histories. Reviewers who have a checklist item about query behavior and transaction scope are more likely to ask about data size, indexes, and expected response times rather than treating this change as a small internal detail.
Risks Checked By A Structured Review
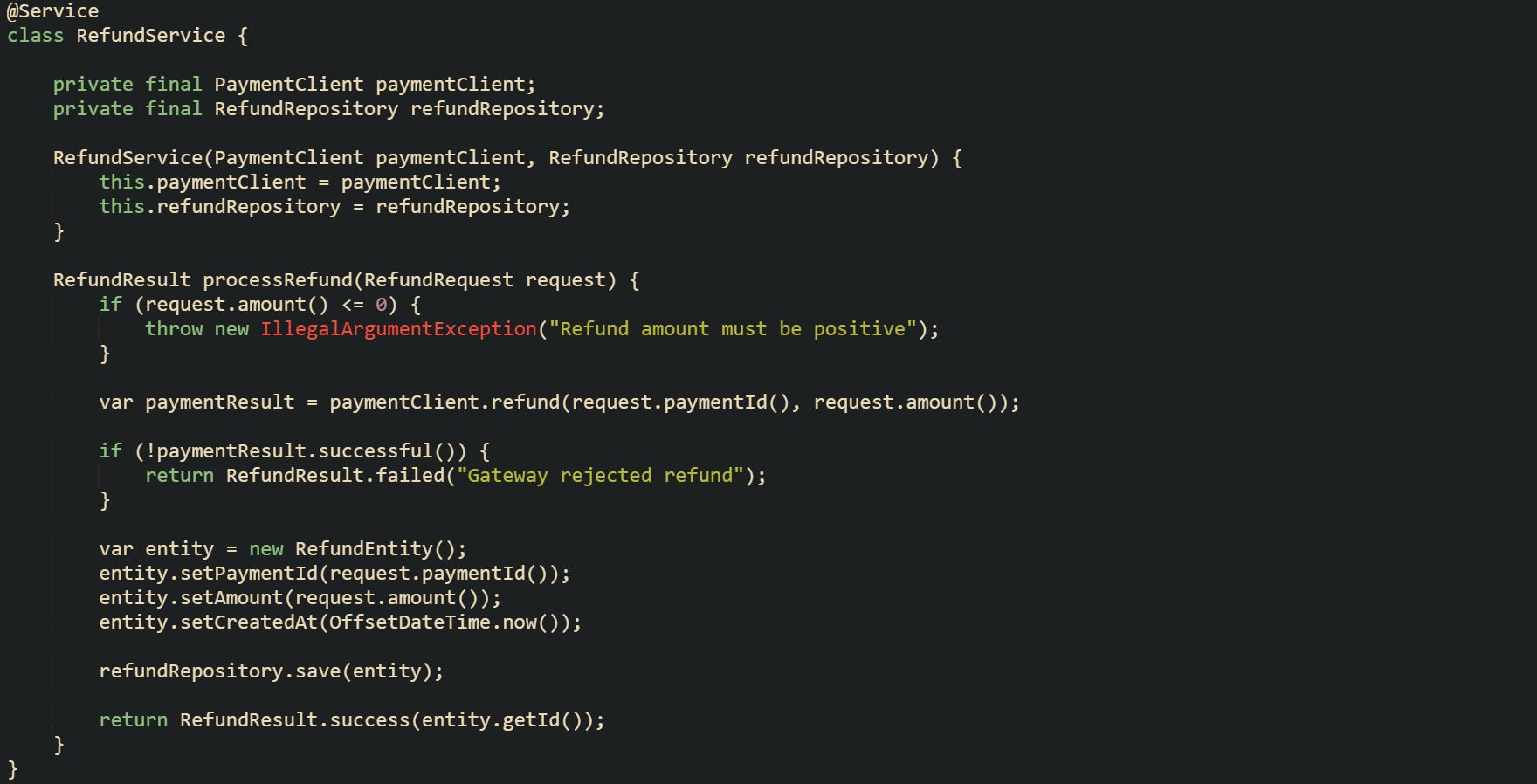
Risk in a Spring Boot backend rarely comes from syntax alone. Logical errors, missing checks, and weak operational visibility appear in areas that a consistent checklist can bring into view on every pull request. Reviewers spend most of their attention checking that the service logic actually does what it’s supposed to do. For a method that gathers data, performs calculations, and updates state, reviewers need to see how branch conditions handle edge cases and error paths. One service that processes refunds can serve as a small example:
Reviewers working from a checklist will look for boundary checks on amount, handling of failed calls to paymentClient, and correct persistence in refundRepository. Changes in a pull request that remove error checks or skip saving a record can be spotted quickly when this category is always on the review list.
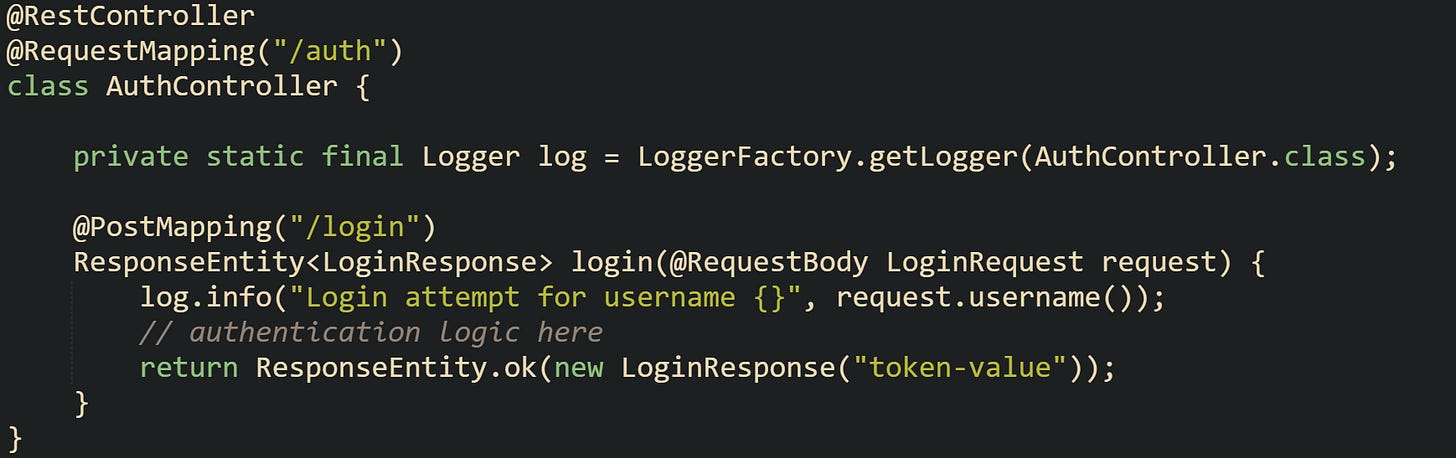
Data protection and security form a common risk area. Spring Security, validation, and logging meet at the edges of a Spring Boot service. Pull requests that add a new controller with an @PreAuthorize expression should trigger questions about authentication and authorization. Code that logs incoming requests or database entities must avoid exposing sensitive data, like:
Checklists that mention security prompt reviewers to confirm that passwords are not written to logs, that authentication logic integrates with the existing security configuration, and that new endpoints respect established access rules instead of bypassing them.
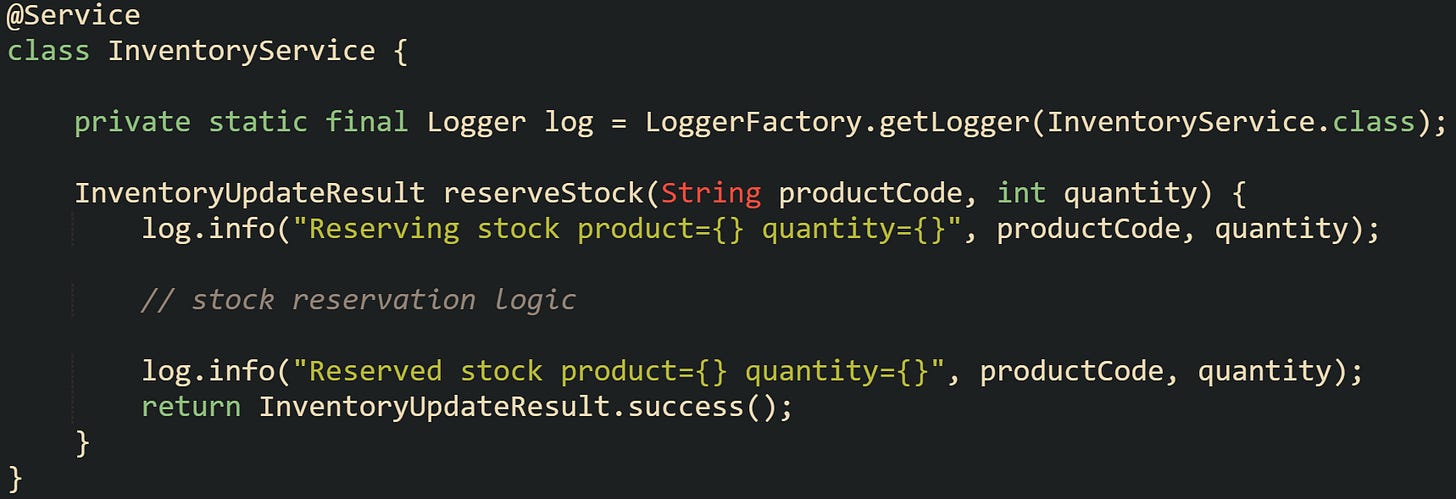
Operational visibility brings logs, metrics, and trace ids into the picture. When an incident occurs in production, engineers lean on those tools first. Pull requests that adjust flows without updating logs or metrics reduce that visibility. Small adjustments to logging can bring a change back into line with the rest of the service:
Readers with a checklist in hand will ask whether log lines include stable identifiers, whether log levels match the impact of the event, and whether this service also records metrics or traces that match existing dashboards.
Documentation risk rounds out this picture. Spring Boot backends sit in a wider environment of API consumers, operational practices, and shared conventions. Pull requests that change public HTTP endpoints, database schemas, or operational flags need matching updates in READMEs, OpenAPI definitions, ADRs, or runbooks. Checklists that always ask about documentation push authors to adjust those artifacts at the same time as code, so future readers see a consistent view of how the service behaves.
Practical Pull Request Checklist For Spring Boot Backends
Spring Boot 3 requires Java 17 or newer, and servlet web projects commonly pull in starters such as spring-boot-starter-web, spring-boot-starter-data-jpa, spring-boot-starter-security, spring-boot-starter-actuator, and spring-boot-starter-test. Checklists that focus on tests, logs, metrics, and documentation give reviewers a repeatable set of checks to run on every pull request.
Test Coverage For Backend Changes
Reviewers who open a pull request usually want to know quickly how much safety the tests provide. Backend services draw on several layers of tests, starting with narrow unit tests around business rules, then web or data slice tests, and finally full context tests where configuration, filters, and beans interact.
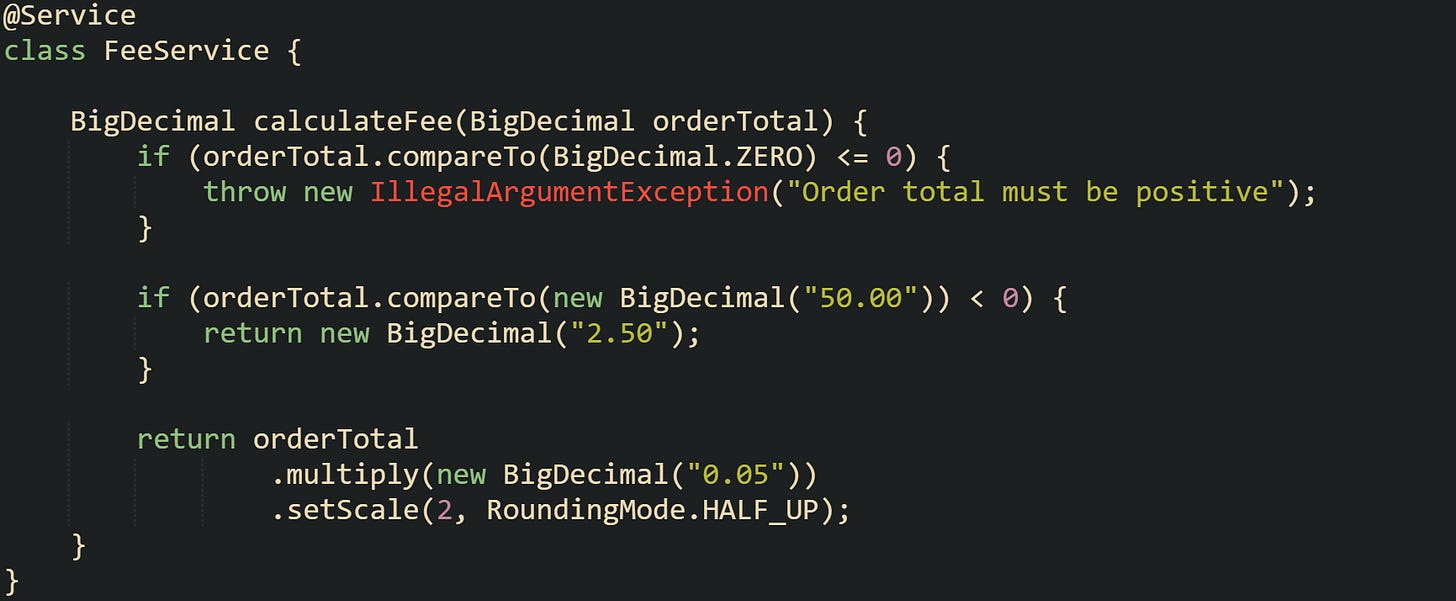
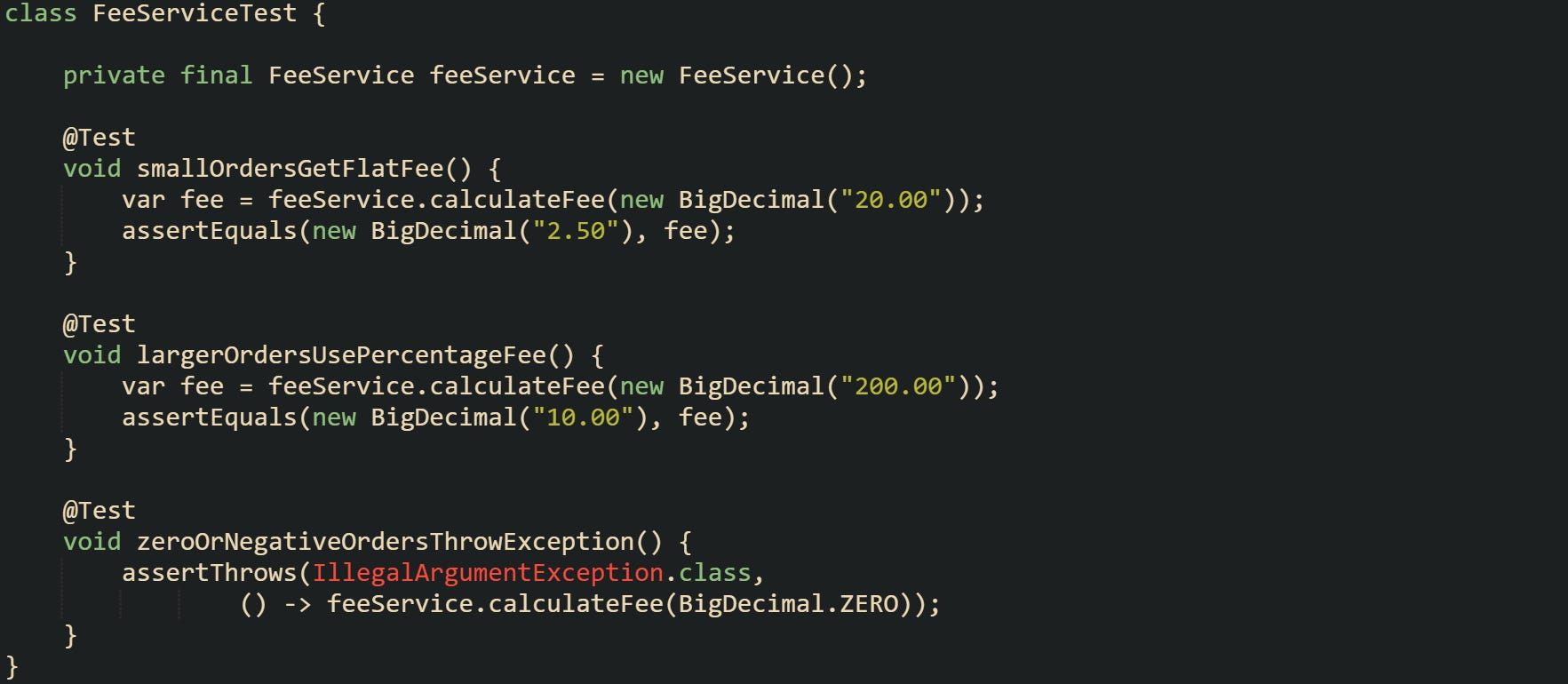
Business logic in service classes is a natural place to start. Let’s consider a service that calculates a fee for an order total:
This method rejects invalid totals and has two branches for different ranges of order values, which gives reviewers specific cases to look at when the logic changes.
Unit tests for that service can spell out expectations in a way that is easy to scan during review:
These tests cover normal values and edge cases, so when a pull request touches fee rules, reviewers can quickly see where expectations sit and whether new branches need extra tests.
HTTP behavior lives at the border with clients, so web tests form an important piece of the checklist as well. Spring MVC controllers integrate nicely with @WebMvcTest and MockMvc, which let reviewers see how request bodies, headers, and status codes behave.
This test makes it very plain what the client sends, which endpoint handles the request, and which status code the controller returns, so a reviewer can judge quickly whether a pull request keeps those behaviors intact.
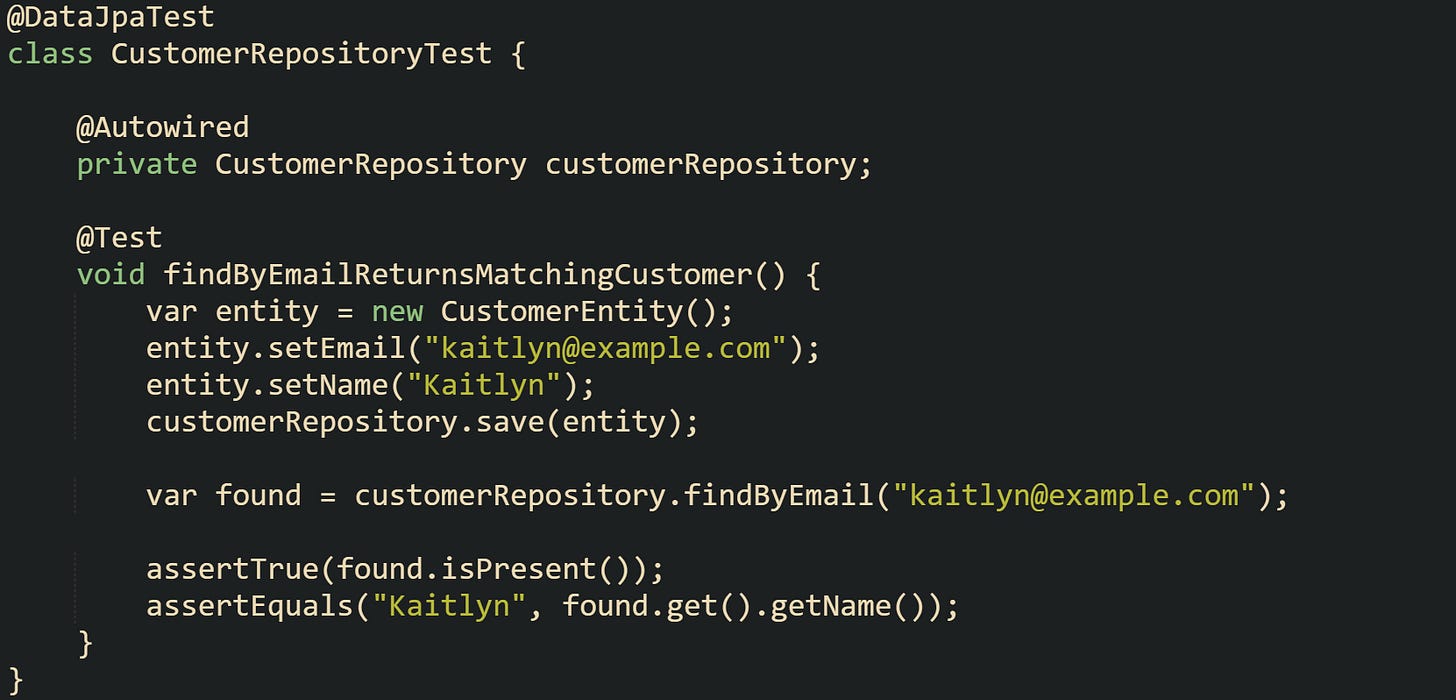
Data access code benefits from its own slice tests. Spring Boot supports @DataJpaTest for JPA repositories, which start a narrow context with in memory database support.
Tests like this give reviewers confidence that repository queries return the expected records and that basic constraints such as uniqueness and case handling match how the code will behave against real data.
Full context integration tests have a place when behavior depends on filters, security, exception handlers, and controllers working in sequence. An @SpringBootTest with TestRestTemplate or WebTestClient lets a reviewer see how authentication, routing, validation, and body mapping all interact. Good checklists push reviewers to confirm that all relevant test layers cover a pull request that touches several parts of the stack and that the continuous integration pipeline runs those tests and shows a green build before anyone starts the review.
Logging Quality In New Code
Logs become the first place many engineers look when something breaks, so pull requests that add or change log statements deserve careful attention. Spring based services usually rely on SLF4J with Logback or Log4j2, and the way message text, log levels, and context fields are chosen has a big impact on how easy it is to search and read those logs during an incident.
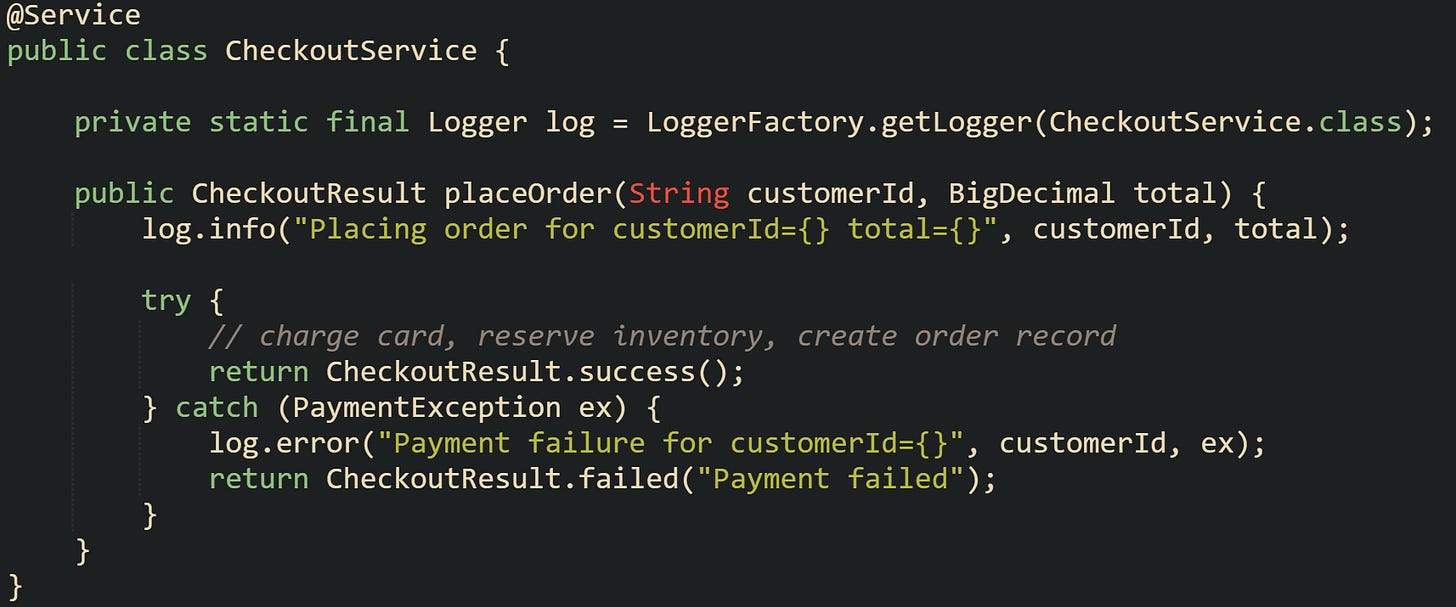
Business flows in service classes are a good place to anchor high value logs. Take this checkout service that processes payments, it can give a sense of what reviewers look for:
This code logs both the start of the checkout and any payment failures, includes a stable identifier, and attaches the exception to the error log. Reviewers reading a pull request that touches placeOrder can check that sensitive data like card numbers never reaches logs, that identifiers stay consistent across services, and that error branches will leave useful information in centralized logging tools.
Controllers handle a lot of input parameters, so developers need to be careful about what reaches the log stream. Reviews should watch for log statements that accidentally capture secrets, raw tokens, or full request objects where toString can print more than intended.
Many Spring Boot services now log in JSON, with fields like traceId, spanId, userId, and operation included on each line. That format helps with dashboards and queries, but only if new log statements follow the same style as existing ones.
Such a log line keeps event names and field names consistent, so alert rules and search queries keep working across services. Pull request checklists that call out log structure help reviewers spot new messages that stray from the expected format or put high volume logs in tight loops where they end up flooding storage.
Metrics For Service Health
Metrics give engineers a window into how a service behaves over time in production, complementing what logs show during specific requests. Spring Boot integrates Micrometer with Actuator, which automatically records timers and counters for HTTP traffic, database usage, JVM memory, and many other pieces. Pull requests can change how those metrics behave whenever they alter endpoint mappings, status codes, or data access patterns, so a checklist that talks about metrics helps reviewers keep an eye on that side of the system.
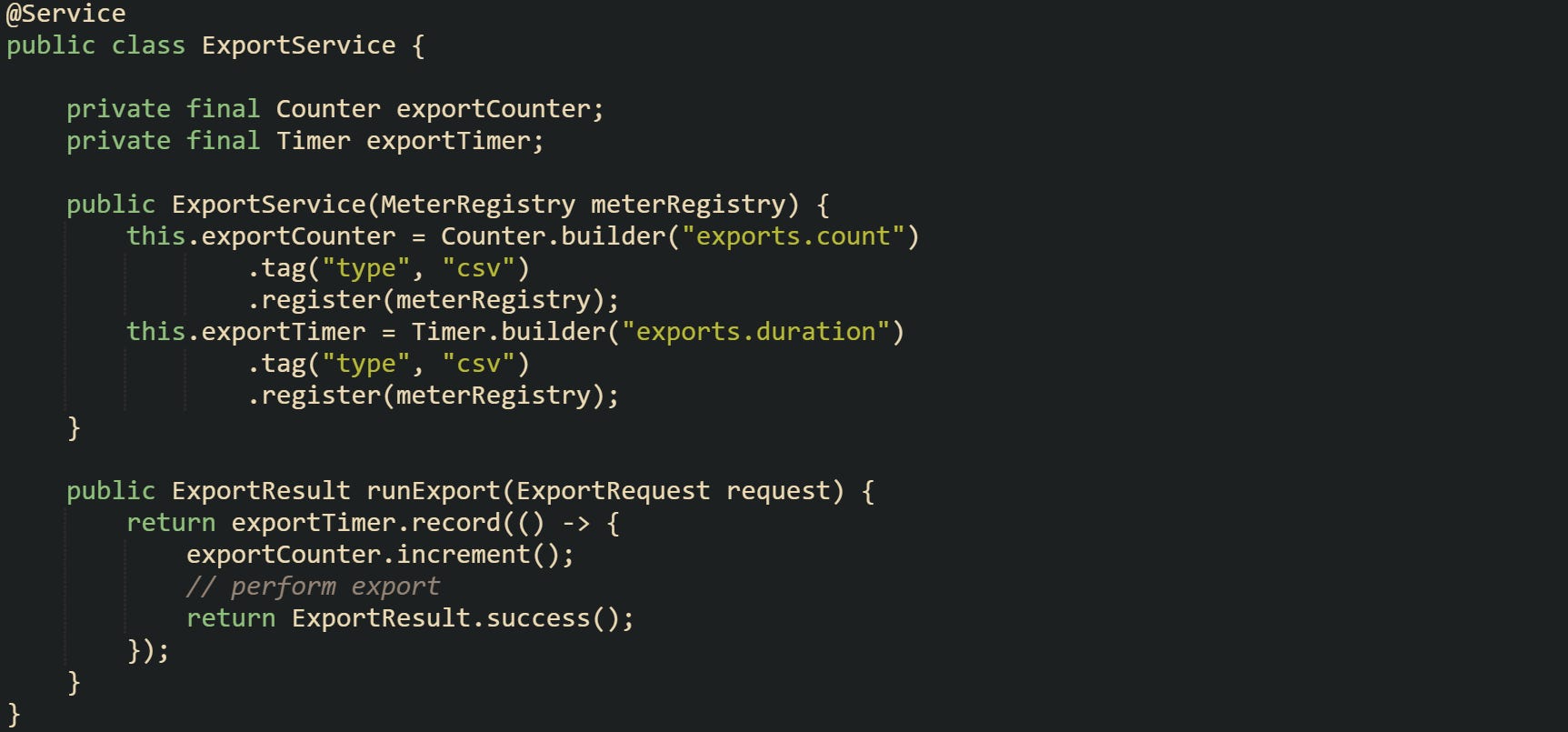
Export services can record how many exports run and how long each one takes:
The code here increments a counter and records the time spent for each export, with a tag that distinguishes CSV exports from other types. Reviewers can look at metric names, tags, and value ranges when they read a pull request and check that new metrics match existing dashboards and alert rules.
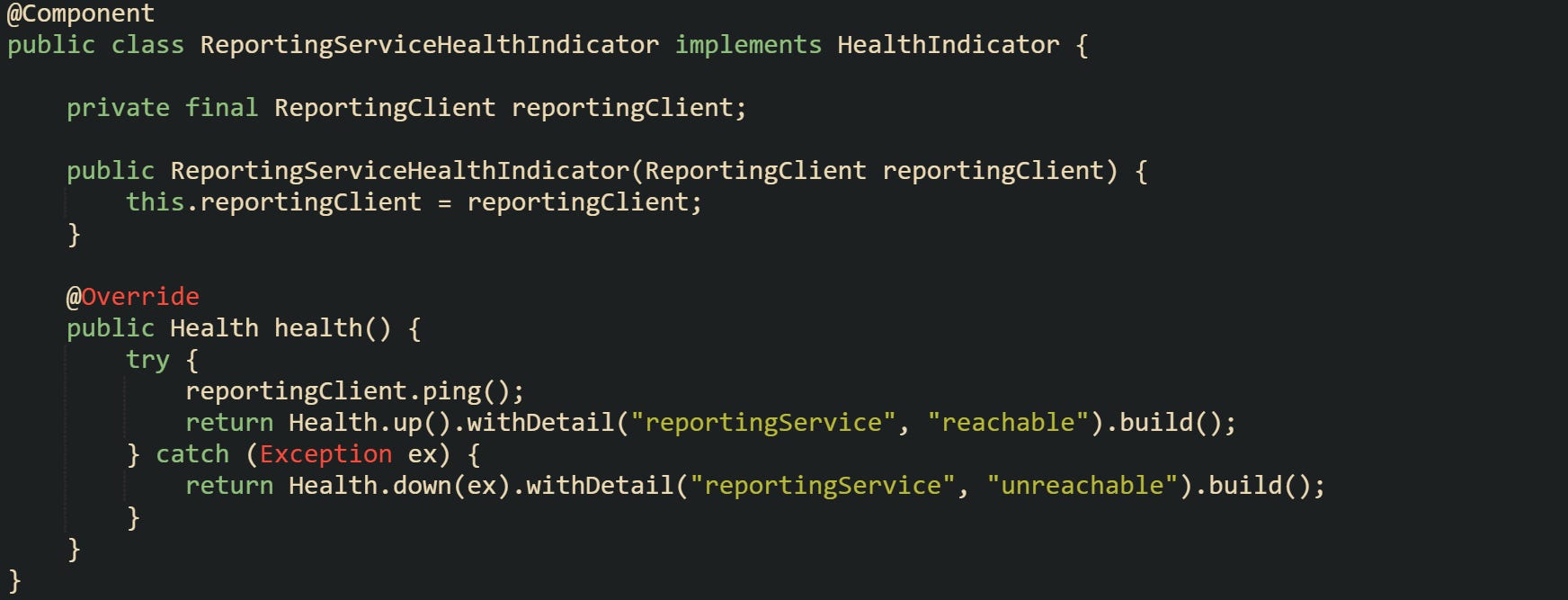
Health indicators use metrics and direct checks to report whether dependencies and subsystems are working. Spring Boot Actuator aggregates health indicators into endpoints such as /actuator/health, which monitoring systems query to decide if an instance is ready or alive. When a pull request connects a new external service, like a reporting API, it can make sense to add a custom health indicator that calls a lightweight endpoint:
Code like this gives a very direct signal about the availability of the downstream system. When reviewers see new outbound dependencies in a pull request, a checklist that mentions health checks can prompt them to ask whether a similar indicator is needed and whether it is wired into readiness or liveness probes.
Documentation Updates
Code that reaches production changes how people develop, deploy, and operate a service, and documentation is where those changes should be recorded. Spring Boot backends usually have several documentation layers, such as README files, OpenAPI specs, ADRs, and operational runbooks. Pull requests that change public endpoints, environment variables, or database structures should update documentation at the same time, not months later when an outage forces someone to dig through history.
Project level docs such as a main README or a docs directory give new engineers and contributors a starting point. These files tend to list Java versions, required backing services like PostgreSQL or Kafka, commands for local runs, and environment variables. When a pull request introduces a new feature flag, adds a dependency on a third party HTTP service, or changes the way a profile works, reviewers can scan the README and check whether those details appear there.
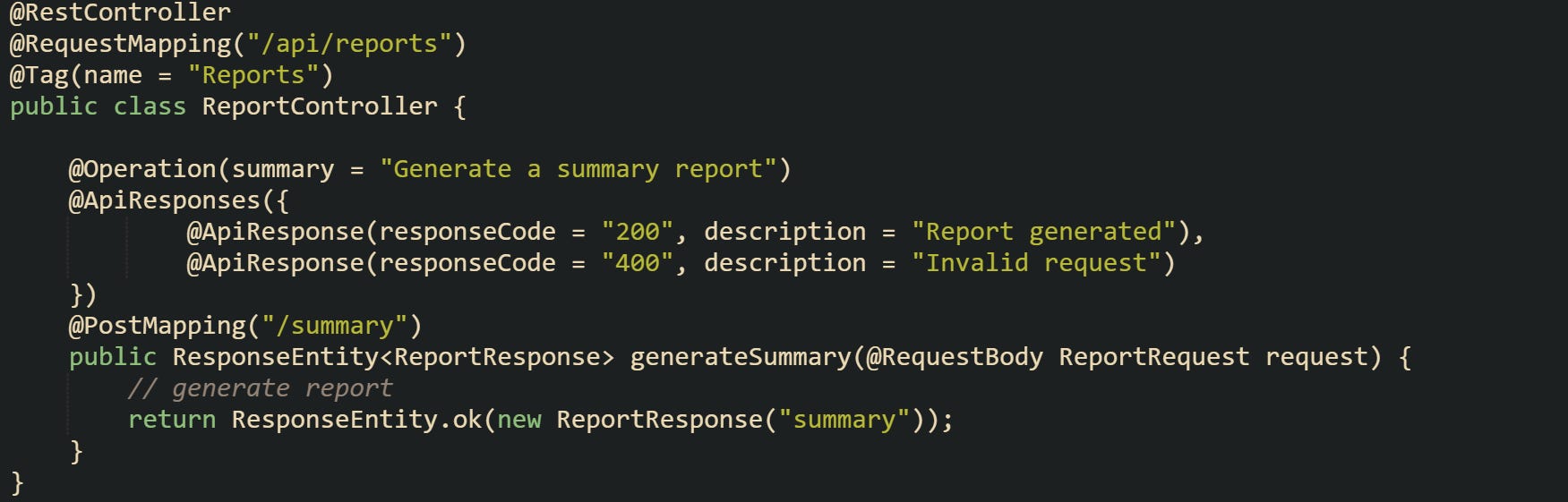
API documentation matters a lot for consumers of the service. Many Spring Boot projects use Springdoc to generate OpenAPI specs from annotations on controllers and models. New or updated endpoints should keep those annotations in sync with actual behavior:
These annotations document response codes and basic behavior right next to the controller logic, which helps reviewers line up what clients see with what the code actually returns when changes arrive.
Operational documentation such as runbooks for on call engineers stays closely tied to what a pull request changes. When new metrics, alerts, or failure modes appear, someone should add short guidance on what each alert means, which dashboards to check, and which steps to try first. Many groups keep a pull request template that asks for a short summary of the change, a test plan, and any manual deployment steps. Checklists that call out documentation give reviewers a nudge to look at these places, not just the Java files, before they click approve.
Conclusion
Pull request checklists for Spring Boot backends keep attention on the mechanics of controllers, services, repositories, and the way they interact with data, logs, metrics, and documentation. Reviewers who walk through the same small set of technical checks on every change test coverage for the new flow, log quality, metric and health indicator updates, and matching docs end up tying each pull request directly to how the service behaves when real traffic reaches it.





Comprehensive breakdown of whatmakes PR reviews actually useful instead of just rubber stamps. The emphasis on operational visibility (logs, metrics, health checks) alongside code correctness is something that gets overlooked way too often. I've seen teams skip the documentation piece and pay for it later when troubleshooting.